If you are interested to learn about the Digital Signature
Protecting our IT environment is very critical. Every organization needs to take cybersecurity very seriously. There are numbers of hacking attacks which affecting businesses of all sizes. Hackers, malware, viruses are some of the real security threats in the virtual world. It is essential that every company is aware of the dangerous security attacks and it is necessary to keep themselves secure. There are many different aspects of the cyber defense may need to be considered. Here are six essential tools and services that every organization needs to consider to ensure their cybersecurity is as strong as possible. They are described below:
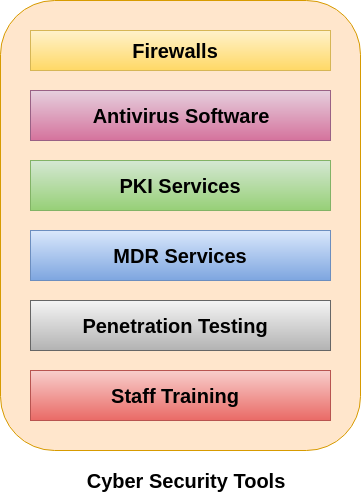
1. Firewalls
As we know, the firewall is the core of security tools, and it becomes one of the most important security tools. Its job is to prevent unauthorized access to or from a private network. It can be implemented as hardware, software, or a combination of both. The firewalls are used to prevent unauthorized internet users from accessing private networks connected to the Internet. All messages are entering or leaving the intranet pass through the firewall. The firewall examines each message and blocks those messages that do not meet the specified security criteria.
The Firewall is very useful, but it has limitations also. A skilled hacker knew how to create data and programs that are believing like trusted firewalls. It means that we can pass the program through the firewall without any problems. Despite these limitations, firewalls are still very useful in the protection of less sophisticated malicious attacks on our system.
2. Antivirus Software
Antivirus software is a program which is designed to prevent, detect, and remove viruses and other malware attacks on the individual computer, networks, and IT systems. It also protects our computers and networks from the variety of threats and viruses such as Trojan horses, worms, keyloggers, browser hijackers, rootkits, spyware, botnets, adware, and ransomware. Most antivirus program comes with an auto-update feature and enabling the system to check for new viruses and threats regularly. It provides some additional services such as scanning emails to ensure that they are free from malicious attachments and web links.
3. PKI Services
PKI stands for Public Key Infrastructure. This tool supports the distribution and identification of public encryption keys. It enables users and computer systems to securely exchange data over the internet and verify the identity of the other party. We can also exchange sensitive information without PKI, but in that case, there would be no assurance of the authentication of the other party. People associate PKI with SSL or TLS. It is the technology which encrypts the server communication and is responsible for HTTPS and padlock that we can see in our browser address bar. PKI solve many numbers of cybersecurity problems and deserves a place in the organization security suite.
PKI can also be used to:
- Enable Multi-Factor Authentication and access control
- Create compliant, Trusted Digital Signatures.
- Encrypt email communications and authenticate the sender’s identity.
- Digitally sign and protect the code.
- Build identity and trust into IoT ecosystems.
4. Managed Detection and Response Service (MDR)
Today’s cybercriminals and hackers used more advanced techniques and software to breach organization security So, there is a necessity for every businesses to be used more powerful forms of defences of cybersecurity. MDR is an advanced security service that provides threat hunting, threat intelligence, security monitoring, incident analysis, and incident response. It is a service that arises from the need for organizations (who has a lack of resources) to be more aware of risks and improve their ability to detect and respond to threats. MDR also uses Artificial Intelligence and machine learning to investigate, auto detect threats, and orchestrate response for faster result.
The managed detection and response has the following characteristics:
- Managed detection and response is focused on threat detection, rather than compliance.
- MDR relies heavily on security event management and advanced analytics.
- While some automation is used, MDR also involves humans to monitor our network.
- MDR service providers also perform incident validation and remote response.
5. Penetration Testing
Penetration testing, or pen-test, is an important way to evaluate our business’s security systems and security of an IT infrastructure by safely trying to exploit vulnerabilities. These vulnerabilities exist in operating systems, services and application, improper configurations or risky end-user behavior. In Penetration testing, cybersecurity professionals will use the same techniques and processes utilized by criminal hackers to check for potential threats and areas of weakness.
A pen test attempts the kind of attack a business might face from criminal hackers such as password cracking, code injection, and phishing. It involves a simulated real-world attack on a network or application. This tests can be performed by using manual or automated technologies to systematically evaluate servers, web applications, network devices, endpoints, wireless networks, mobile devices and other potential points of vulnerabilities. Once the pen test has successfully taken place, the testers will present us with their findings threats and can help by recommending potential changes to our system.
6. Staff Training
Staff training is not a ‘cybersecurity tool’ but ultimately, having knowledgeable employees who understand the cybersecurity which is one of the strongest forms of defence against cyber-attacks. Today’s many training tools available that can educate company’s staff about the best cybersecurity practices. Every business can organize these training tools to educate their employee who can understand their role in cybersecurity.
We know that cyber-criminals continue to expand their techniques and level of sophistication to breach businesses security, it has made it essential for organizations to invest in these training tools and services. Failing to do this, they can leave the organization in a position where hackers would be easily targeted their security system. So, the expense of the investment on these training tools might put a reward for the business organization with long-term security and protection.
How Important Is Cybersecurity?
The importance of cybersecurity can be understood through the research performed by Mimecast. It says that there is a 26% rise in the ransomware, 88% of companies saw email-based spoofing, and 67% of the organizations have reported that there is an increase in impersonation fraud.
Making use of public Wi-Fi makes your device or data more vulnerable to the attacks. According to the research performed by Norton, 54% of internet users use public Wi-Fi and 73% of people knew that public Wi-Fi is not safe even if it is passwords protected. All these statistics prove that cybersecurity is the need of the hour.
Open Source Software Cyber Security Tools
The best things in life are free and open-source software is one of them. Security at data and network-level is greatly enhanced by these software tools which open the door to a more safe and secure cyber world.
1. Gnu PG: Guarding Your Privacy
The GNU Privacy Guard/GPG is a tool that is used for file and email encryption. A strong encryption measure will provide immense security at the data level. This is a viable open-source alternative to PGP or Pretty Good Privacy. It complies with Open PGP standards.
This is a command-line tool part of major Linux offerings such as Ubuntu, OpenSUSE, CentOS, and Fedora. So, throw your hat in the ring today and use this amazing tool to protect data by using GPG to generate public and private keys in the backup server and import the port key to all data servers from where the backup has to be taken and encrypt it.
2. Truecrypt: A Real Solution
Many open source utilities are there for disk-level encryption. Truecrypt is perfect for disk-level encryption. This open-source security tool is used for on the fly disk encryption. This handy tool is the correct choice because Truecrypt encrypts automatically before data is saved on the disk and decrypts it completely after it is loaded from the disk sans user intervention. Popular Course in this category
3. Open Web Application Security Project: Combating Web Vulnerabilities
Application security is as critical as other levels of security because just as web presence and development is increasing, web vulnerabilities are also rising. Application security is important. OWASP is an open-source web app security project which provides best practices and code review steps among other guidelines that developers, architects, and designers can use to develop secure software.
4. ClamAV: The Perfect Antivirus Tool

Host level security offers protection for single devices such as servers PCs and laptops. ClamAV is the perfect antivirus system to scan data emanating from different sources. This is an open-source antivirus designed for catching malware, viruses and deadly Trojans which attempt to steal information.
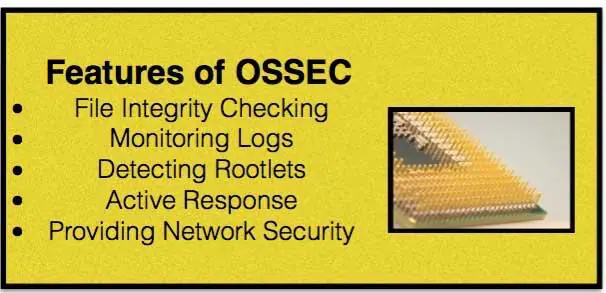
5. OSSEC: Integrating Security Needs
Open Source SECurity is an open-source tool that provides SIM and SEM solutions as well as log monitoring. This is an open-source HIDS or Home Based Intrusion Detection System. OSSEC helps customers to meet standards and integrate Security Incident Management and Security Event Management.
6. Snort: IDS/IPS Tool with a Difference
Snort is an open-source network IDS/IPS (Intrusion Detection and Prevention System) which performs detection and analysis of network traffic moving across in a more detailed way than an average firewall. IDS and IPS tools are known for analyzing traffic and comparing the packet to a database of previous or known attack profiles. IDS tools alert IT staff regarding attacks, but IPS systems go a step further-they block harmful traffic. A blend of the two is an essential part of a comprehensive security architecture.
7. OpenVAS: Providing Comprehensive Vulnerability Scanning
OpenVAS is a framework of services and tools offering intensive vulnerability scanning as well as management systems. It is the open-source version of Nessus. Vulnerability management can be added to patch and configuration management plus antivirus software for blocking/destroying malware.
8. BackTrack: On the Right Path
This well known Linux based security distribution is employed for penetration testing. This offers a one-stop solution for security needs and comprises more than 300 OSS tools categorized into different areas.
9. OSSIM: All in One Security Solution
Open Source Security Information Management provides for a Security Information and Event Management solution that has integrated open-source software’s Snort, OpenVAS, Mrtg, NTOP, and Nmap. This is a cost-effective solution for monitoring the health and security of network/hosts.
10. IPCop: Protecting the Perimeter
Perimeter…it is the final frontier where the network ends and internet security commences. Perimeter comprises one/more firewalls for protecting the network. IPCop is a Linux based firewall distribution configured and made to protect the network. It can run on individual machines or behind the ISP network. Other functionalities offered by IPCop include the DNS server, Proxy server, and DHCP server.


